Breach Resolution Advances
In a significant development within the cybersecurity landscape, a company has reached an agreement with malicious actors responsible for two separate
security breaches. This resolution marks a crucial step in addressing the aftermath of these intrusions, underscoring the complex nature of cyber conflict and the innovative strategies being employed to navigate and mitigate such incidents. The agreement highlights a shift towards resolution and recovery, demonstrating that organizations are increasingly seeking pragmatic solutions to cyber threats rather than solely focusing on punitive measures. This approach often involves understanding the motives and methods of attackers to prevent future occurrences and build more robust defense mechanisms, reflecting a mature understanding of the ongoing battle against digital adversaries.
AI for Cyber Defense
A notable startup has secured substantial Series B funding, amassing $125 million, to advance its artificial intelligence-powered solutions for real-time cyberattack detection and prevention. This significant investment signals a strong market confidence in AI's potential to revolutionize cybersecurity by enabling systems to identify and neutralize threats as they emerge. The company aims to develop sophisticated AI models capable of analyzing vast amounts of data to spot anomalous patterns indicative of malicious activity. Such proactive defense strategies are becoming increasingly vital as cyber threats grow more complex and rapid, moving beyond traditional signature-based detection methods to adaptive and intelligent security frameworks that can learn and respond dynamically to evolving attack vectors.
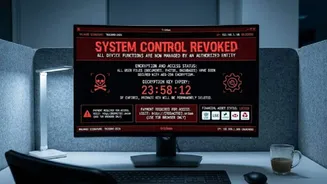
Data Privacy Concerns
A recent incident involving a US bank has brought to light security lapses that occurred when customer data was inadvertently shared with an artificial intelligence application. This disclosure serves as a stark reminder of the potential risks associated with integrating new technologies, particularly AI, into data handling processes. It emphasizes the critical need for stringent protocols and thorough vetting of third-party applications to safeguard sensitive personal information. The event underscores the ongoing challenge of balancing innovation with robust data protection, prompting a re-evaluation of how organizations manage and share data in an increasingly interconnected digital environment, especially when employing advanced tools that process such information.
Enhanced Mobile Security
A leading technology firm has introduced a novel security feature for its mobile operating system, designed to assist users in identifying and combating sophisticated spyware attacks. This new functionality represents a proactive effort to bolster user privacy and device integrity by providing enhanced visibility into potential surveillance threats. By equipping users with tools to detect hidden malicious software, the aim is to empower individuals to take control of their digital security. This initiative reflects a growing trend towards user-centric security solutions, acknowledging that effective defense requires not only robust system-level protection but also informed and vigilant end-users capable of recognizing and responding to emerging cyber risks on their devices.