What's Happening?
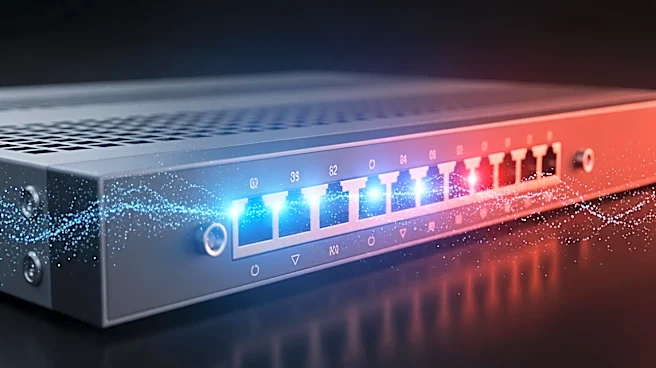
Palo Alto Networks has disclosed a zero-day vulnerability, CVE-2026-0300, affecting its firewalls, which has been exploited in a campaign suspected to be linked to Chinese state-sponsored hackers. The vulnerability allows unauthenticated remote code execution
with root privileges. The attack, attributed to a likely state-sponsored group CL-STA-1132, involved tools like Earthworm and ReverseSocks5, commonly used by Chinese APT groups. The attackers conducted log cleanup and Active Directory enumeration to avoid detection. Patches are expected to be released soon, with mitigations provided in the interim.
Why It's Important?
This incident highlights the ongoing threat of state-sponsored cyberattacks targeting critical infrastructure and technology companies in the U.S. The use of zero-day vulnerabilities by suspected Chinese hackers underscores the sophistication and persistence of these threats. The exploitation of such vulnerabilities can lead to significant security breaches, affecting businesses and potentially national security. The incident also emphasizes the need for robust cybersecurity measures and international cooperation to address and mitigate cyber threats.
What's Next?
Palo Alto Networks plans to release patches for the vulnerability, with interim mitigations already in place. The cybersecurity community will likely increase monitoring for similar attacks and enhance defenses against state-sponsored threats. This incident may prompt further investigations into the activities of Chinese APT groups and their impact on global cybersecurity. Organizations are expected to review and strengthen their security protocols to prevent similar breaches.