What's Happening?
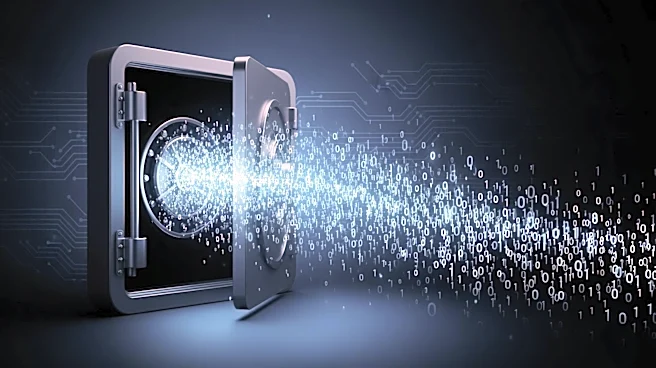
A recent analysis highlights that simply changing passwords in Active Directory (AD) environments does not fully mitigate security breaches. Attackers can exploit a brief window where old credentials remain valid due to cached password hashes and synchronization
delays with Entra ID. This gap allows attackers to maintain access or re-establish a foothold. The report emphasizes the need for comprehensive security measures beyond password resets, such as invalidating active sessions and rotating service account passwords. The study also points out that attackers can use techniques like pass-the-hash and Kerberos ticket attacks to bypass password changes.
Why It's Important?
The findings underscore the critical need for robust security protocols in AD environments, as password resets alone are insufficient to thwart sophisticated cyber threats. With stolen credentials involved in nearly 45% of breaches, organizations must adopt comprehensive strategies to protect sensitive data. This includes implementing secure password policies, frequent synchronization, and auditing access control lists. The report serves as a wake-up call for IT administrators to enhance their incident response strategies and close potential security gaps that could be exploited by attackers.
What's Next?
Organizations are encouraged to adopt a multi-layered security approach, including the use of tools like Specops uReset for secure password resets and immediate updates to cached credentials. IT teams should also focus on terminating active sessions and clearing Kerberos tickets to prevent unauthorized access. Regular audits of group memberships and privileged accounts are recommended to identify and eliminate potential backdoors. As cyber threats evolve, continuous monitoring and adaptation of security measures will be crucial to safeguarding organizational assets.