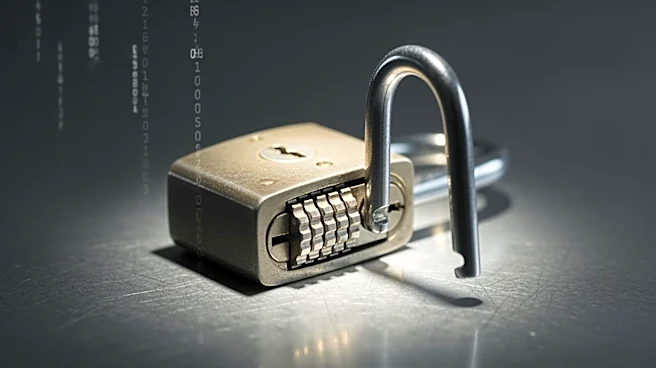
What's Happening?
A critical vulnerability has been identified in OpenSSH, a widely used tool for remote server management. The flaw, designated as CVE-2026-35414, affects versions prior to 10.3 and involves the mishandling of the authorized_keys principals option in specific
scenarios. This vulnerability could allow attackers to gain root access to affected servers, enabling them to execute commands, steal data, or disrupt operations. The Centre for Cybersecurity Belgium has issued a warning, urging organizations to update to the latest version of OpenSSH to mitigate potential risks. Although no active exploitation has been reported, the vulnerability has been present in nearly all OpenSSH versions released over the past 15 years.
Why It's Important?
The discovery of this vulnerability is significant due to the widespread use of OpenSSH in managing servers across various industries. A successful exploit could have severe consequences, including unauthorized access to sensitive information, system tampering, and operational disruptions. This poses a substantial threat to businesses, potentially leading to financial losses and reputational damage. The urgency of the situation is underscored by the recommendation to prioritize patching and enhance monitoring capabilities to detect any suspicious activities. Organizations that fail to address this vulnerability may face increased risks of cyberattacks and data breaches.
What's Next?
Organizations are advised to immediately update their OpenSSH installations to version 10.3 or later to protect against potential exploits. In addition to patching, it is recommended to implement host-based intrusion detection and file integrity monitoring systems to identify signs of compromise. The Centre for Cybersecurity Belgium also suggests reporting any incidents of intrusion to facilitate a coordinated response. As the cybersecurity landscape evolves, maintaining up-to-date software and robust security measures will be crucial in safeguarding against emerging threats.