What's Happening?
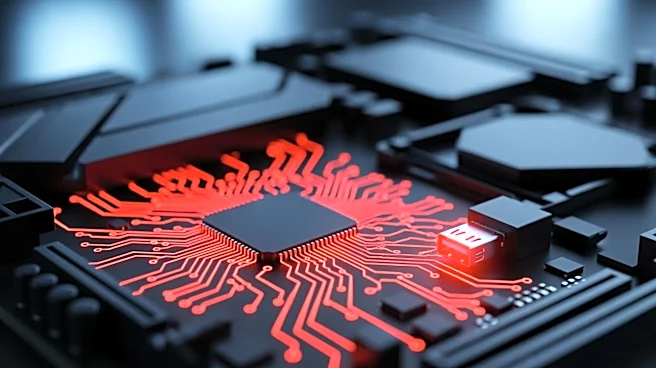
China-aligned hackers have been identified using a Linux-based ELF backdoor to steal cloud credentials from major cloud service providers such as AWS, GCP, Azure, and Alibaba Cloud. According to Breakglass Intelligence, the hackers employ a 'zero-detection'
technique that utilizes SMTP port 25 as a covert command-and-control (C2) channel. This method allows them to harvest cloud provider credentials and metadata without being detected by conventional scanning tools like Shodan and Censys. The stolen credentials are then sent to three Alibaba-themed typosquatted domains hosted on Alibaba Cloud infrastructure in Singapore. This sophisticated approach highlights the evolving tactics of cybercriminals in targeting cloud environments.
Why It's Important?
The breach underscores the vulnerabilities in cloud security, particularly the exploitation of cloud credentials, which can lead to significant data breaches and financial losses for businesses. As cloud services become integral to business operations, the security of these platforms is paramount. The use of typosquatting and covert channels by hackers indicates a growing sophistication in cyberattacks, posing a threat to the integrity and confidentiality of sensitive data stored in the cloud. This incident serves as a wake-up call for organizations to enhance their security measures and remain vigilant against such advanced threats.
What's Next?
Organizations using cloud services are likely to reassess their security protocols and invest in more robust detection and response systems to prevent similar breaches. Cloud service providers may also enhance their security features and offer additional tools to help clients protect their credentials. Regulatory bodies might consider implementing stricter guidelines for cloud security to safeguard against such attacks. The cybersecurity community will likely focus on developing new strategies to detect and mitigate these sophisticated threats.
Beyond the Headlines
This incident highlights the ethical and legal challenges in cybersecurity, particularly in attributing attacks to state-sponsored actors. The use of typosquatting and covert channels raises questions about the responsibility of cloud service providers in preventing such abuses. Additionally, the incident may influence international relations, as cyberattacks attributed to state actors can escalate tensions between countries. Long-term, this could lead to increased collaboration between nations to establish norms and agreements on cybersecurity.