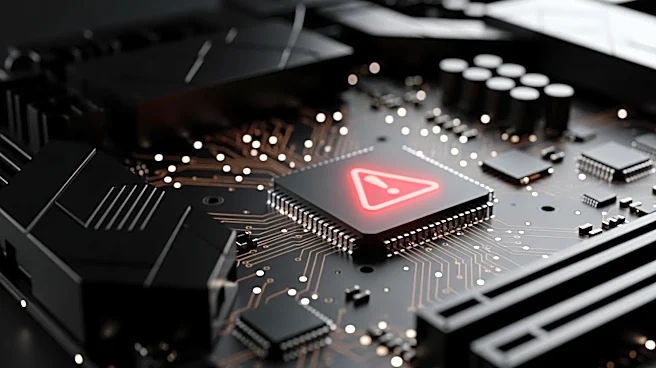
What's Happening?
Palo Alto Networks is set to release patches for a critical zero-day vulnerability, identified as CVE-2026-0300, affecting its PAN-OS software on PA and VM series firewalls. This vulnerability, a buffer overflow in the User-ID Authentication Portal (Captive
Portal) service, allows unauthenticated attackers to execute malicious code with root privileges. The company plans to release the first round of patches on May 13, followed by a second round on May 28. The flaw has been exploited in limited, targeted attacks, likely by sophisticated threat actors, including state-sponsored groups. Palo Alto Networks has advised that limiting access to the User-ID Authentication Portal to trusted internal IPs can significantly reduce the risk of exploitation. Notably, Prisma Access, Cloud NGFW, and Panorama appliances are not affected by this vulnerability.
Why It's Important?
The exploitation of this zero-day vulnerability highlights the ongoing threat posed by sophisticated cyber attackers, particularly those backed by state actors. Palo Alto Networks' firewalls are widely used by major enterprises and government organizations, making them attractive targets for such attacks. The timely release of patches is crucial to mitigate potential security breaches that could compromise sensitive data and disrupt operations. This incident underscores the importance of robust cybersecurity measures and the need for organizations to stay vigilant against emerging threats. The vulnerability's exploitation also reflects broader trends in cybersecurity, where attackers increasingly target critical infrastructure and high-value assets.
What's Next?
Palo Alto Networks will release the first set of patches on May 13, with a second round expected on May 28. Organizations using affected firewalls are advised to apply these patches promptly to protect against potential exploitation. The cybersecurity community will likely monitor the situation closely, and further advisories may be issued as more information becomes available. Additionally, the inclusion of this vulnerability in CISA’s Known Exploited Vulnerabilities catalog could prompt further action from regulatory bodies and industry stakeholders to enhance cybersecurity defenses.