What's Happening?
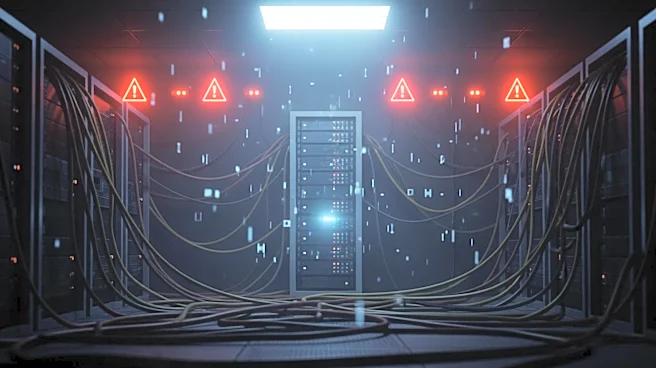
Progress Software has released patches for several critical vulnerabilities in its MOVEit WAF and LoadMaster products. These vulnerabilities, identified as CVE-2026-3517, CVE-2026-3518, CVE-2026-3519,
and CVE-2026-4048, could allow remote code execution and OS command injection. The flaws are primarily due to improper input sanitization in various commands and APIs. Progress has urged users to update to the latest versions to mitigate potential security risks. The company has not received reports of these vulnerabilities being exploited but emphasizes the importance of timely updates to protect against potential threats.
Why It's Important?
The patching of these vulnerabilities is crucial for maintaining the security integrity of systems using MOVEit WAF and LoadMaster. Unpatched systems could be susceptible to unauthorized access and control, posing significant risks to data security and operational continuity. This development highlights the ongoing challenges in cybersecurity, where timely identification and resolution of vulnerabilities are essential to protect sensitive information and infrastructure. Organizations using these products must prioritize updates to safeguard against potential exploitation.
What's Next?
Organizations using MOVEit WAF and LoadMaster should promptly apply the patches to secure their systems. Progress Software will likely continue monitoring for any exploitation attempts and may release further updates if necessary. The cybersecurity community will be vigilant in assessing the impact of these patches and any emerging threats. This situation underscores the need for continuous vigilance and proactive measures in cybersecurity management.