What's Happening?
Palo Alto Networks has reported that a critical zero-day vulnerability in its PAN-OS firewall has been exploited by suspected state-sponsored hackers for nearly a month. The vulnerability, identified as CVE-2026-0300, allows unauthenticated attackers
to execute arbitrary code with root privileges on affected firewalls. The exploitation began on April 9, 2026, and involves the use of tools like Earthworm and ReverseSocks5 to establish covert communications and bypass network restrictions. The company is working on releasing patches, with the first expected by May 13.
Why It's Important?
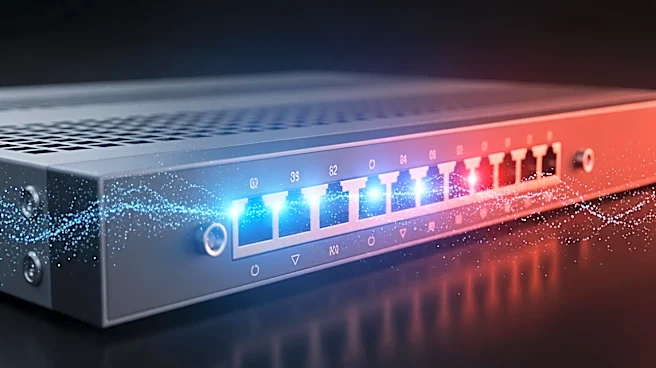
This security breach highlights the ongoing threat posed by state-sponsored cyberattacks targeting critical infrastructure. The exploitation of the PAN-OS firewall vulnerability could have significant implications for organizations relying on these systems for network security. The incident underscores the need for robust cybersecurity measures and timely updates to protect against sophisticated attacks. It also raises concerns about the security of network edge devices, which are increasingly targeted by threat actors.
What's Next?
Palo Alto Networks is expected to release security patches to address the vulnerability. In the meantime, the company advises customers to restrict access to the vulnerable portal or disable it if necessary. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added the vulnerability to its Known Exploited Vulnerabilities Catalog and has mandated federal agencies to secure affected firewalls by May 9. This incident may prompt organizations to reassess their cybersecurity strategies and enhance their defenses against similar threats.