The Bot Blocker
In the vast expanse of the internet, malicious bots are a persistent threat, constantly probing for vulnerabilities and attempting to disrupt services.
To combat this, many websites employ sophisticated security services that act as digital gatekeepers. These services are designed to meticulously examine incoming traffic, differentiating between genuine human users and automated programs. The process typically involves a series of checks that analyze various aspects of your browsing behavior and technical configuration. This proactive approach is crucial for maintaining the integrity and performance of online platforms, safeguarding sensitive data, and preventing unauthorized access. Without these vigilant guardians, the online landscape would be far more susceptible to attacks, leading to widespread disruption and potential harm to users and businesses alike. This verification layer is a fundamental step in ensuring a secure and reliable digital environment for everyone.
Verification in Progress
When you encounter a security verification page, it signifies that the website's defense system is actively assessing your legitimacy as a user. This isn't a random delay; it's a deliberate step to ensure your safety and the stability of the service. The system analyzes a multitude of factors, often in real-time, to build a comprehensive profile of your connection. This could include examining your IP address, browser type and version, operating system, and even subtle behavioral patterns that are characteristic of human interaction. The goal is to identify any anomalies that might suggest automated activity. The process is designed to be as seamless as possible, often resulting in a quick confirmation once your identity as a human is established. This period of 'waiting for response' is a critical moment where your digital footprint is being scrutinized to ensure it aligns with expected user behavior, thereby preventing bots from gaining unauthorized entry.
Behind the Scenes
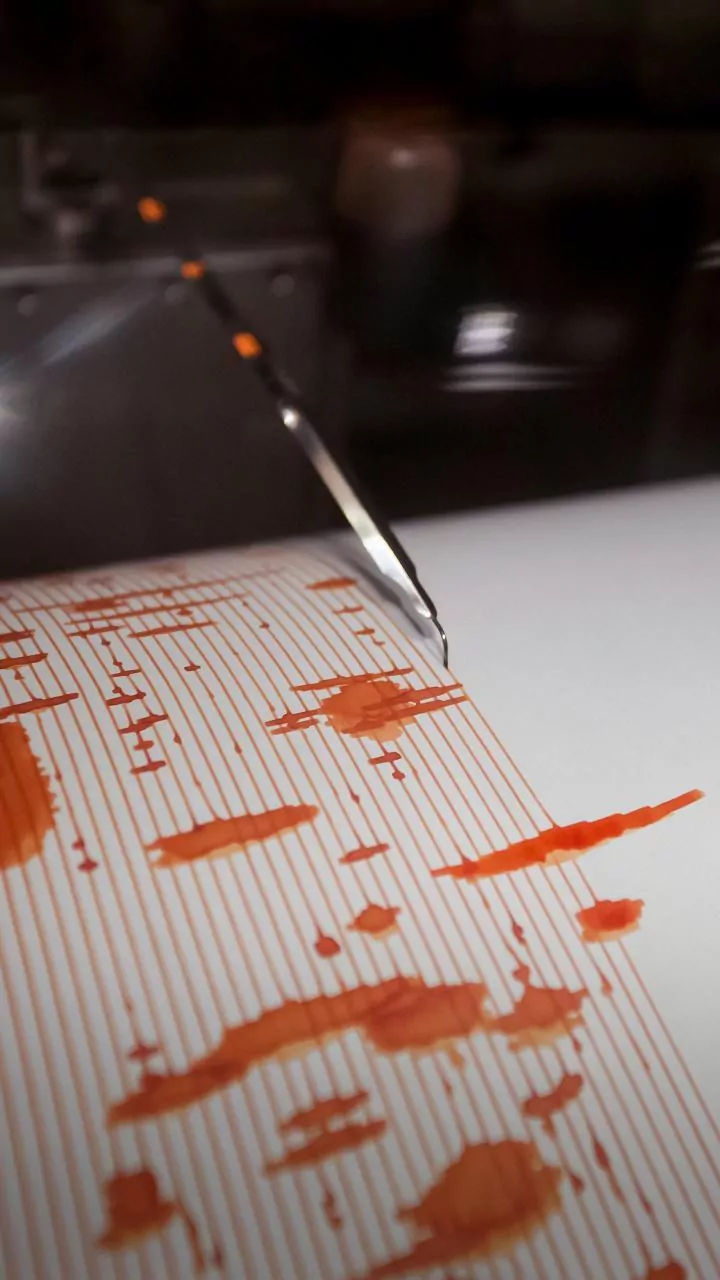
The underlying technology powering these security verifications is incredibly complex, often leveraging advanced artificial intelligence and machine learning algorithms. Services like Cloudflare, which provides 'Performance and Security,' employ a global network of servers to analyze traffic patterns and detect threats. When a verification is triggered, your request is routed through this network, where it undergoes rigorous analysis. This can involve CAPTCHA challenges, JavaScript evaluations, or even analyzing the timing and speed of your interactions. The system continuously learns and adapts, updating its threat detection models to stay ahead of evolving bot technologies. The Ray ID, such as '9eb9d55308f59787,' is a unique identifier for your specific request, allowing the system to track and log the verification process. This intricate dance between user and security service ensures that when you finally gain access, it's to a platform that has taken significant steps to protect you from malicious actors.