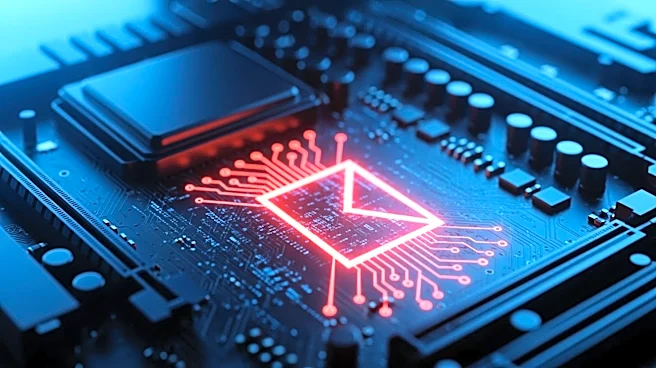
What's Happening?
SentinelLabs researchers have identified a new malware named 'PCPJack' that targets cloud infrastructure by removing malicious code planted by the TeamPCP hackers and replacing it with its own. Discovered on April 28, PCPJack was found through a hunting
rule on Google's VirusTotal service. The malware installs a Python virtual environment and downloads modules to steal credentials from various services, including Docker, Kubernetes, and MongoDB. Unlike typical malware, PCPJack does not deploy cryptocurrency mining software but instead focuses on credential theft and fraud. The malware's worm-like behavior allows it to propagate across cloud environments.
Why It's Important?
The emergence of PCPJack highlights the evolving nature of cyber threats targeting cloud infrastructure. By focusing on credential theft and fraud, the malware poses a significant risk to organizations relying on cloud services for their operations. The ability of PCPJack to propagate within cloud environments underscores the need for robust security measures and monitoring to protect sensitive data and prevent unauthorized access. This development also emphasizes the importance of collaboration between cybersecurity firms and cloud service providers to address vulnerabilities and enhance security protocols.