What's Happening?
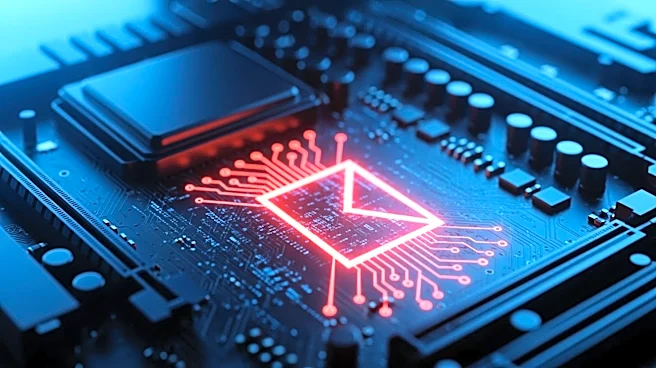
SentinelLabs researchers have identified a new malware, named PCPJack, which targets and removes malicious code planted by the TeamPCP supply chain hackers. Discovered on April 28, PCPJack replaces the existing malware with its own code, creating a Python
virtual environment and downloading modules to execute its functions. The malware is designed to steal credentials from various services, including cloud and container platforms, and exhibits worm-like behavior to propagate across cloud infrastructures. Unlike typical malware, PCPJack does not engage in cryptocurrency mining but focuses on monetizing through credential theft and resale.
Why It's Important?
The emergence of PCPJack underscores the evolving nature of cyber threats, where malware not only disrupts existing malicious operations but also seeks to exploit them for its own gain. This development highlights the complexity of cybersecurity challenges, as attackers continuously adapt their strategies to bypass defenses and maximize their impact. Organizations relying on cloud services must remain vigilant and enhance their security measures to protect against such sophisticated threats. The incident also emphasizes the need for continuous monitoring and threat intelligence to identify and mitigate emerging risks.
What's Next?
Security teams will need to analyze the tactics used by PCPJack to develop effective countermeasures and prevent further exploitation. The cybersecurity community may collaborate to share insights and strategies to combat this new threat. Organizations should review their security protocols and consider implementing advanced threat detection and response solutions to safeguard their cloud environments. As the situation evolves, further research and analysis will be crucial to understanding the full scope and impact of PCPJack's activities.