What's Happening?
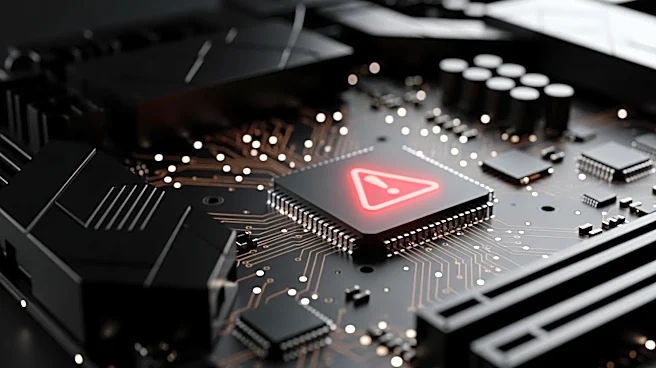
Theori, a cybersecurity company, has identified a significant vulnerability in the Linux operating system, dubbed 'Copy Fail'. This flaw, tracked as CVE-2026-31431, was discovered using Theori's AI-powered penetration testing platform, Xint. The vulnerability affects
all mainstream Linux kernels built since 2017, potentially allowing attackers with authenticated local access to gain root access to systems. Theori's disclosure, which included a proof-of-concept exploit, has been criticized for its lack of technical detail, as it relied heavily on AI-generated content. Despite this, the Cybersecurity and Infrastructure Security Agency has added the vulnerability to its catalog of known exploited vulnerabilities. Theori has stated that patches were issued by major Linux distributions before the public disclosure, but the vulnerability still poses a risk, especially if paired with another exploit to gain initial access.
Why It's Important?
The discovery of the 'Copy Fail' vulnerability highlights the growing role of AI in cybersecurity, both as a tool for identifying threats and as a source of potential misinformation. The vulnerability's potential to allow root access to Linux systems is significant, given the widespread use of Linux in servers and critical infrastructure. The reliance on AI-generated content in Theori's disclosure has raised concerns about the accuracy and reliability of such information, emphasizing the need for thorough human review. Organizations using Linux systems must be vigilant in applying patches and verifying the security of their systems to prevent exploitation. The situation underscores the challenges faced by cybersecurity professionals in balancing the speed of AI-assisted discovery with the need for detailed and accurate reporting.
What's Next?
Organizations are advised to apply the available patches to mitigate the risk posed by the 'Copy Fail' vulnerability. Theori plans to withhold further technical details until the patch is widely adopted, to prevent potential exploitation. Security teams must remain cautious when dealing with AI-generated exploit code, ensuring thorough testing and validation. The incident may prompt a broader discussion within the cybersecurity community about the role of AI in vulnerability disclosure and the importance of maintaining technical rigor in such reports. As AI continues to play a larger role in cybersecurity, companies may need to develop new protocols for integrating AI findings with traditional security practices.