What's Happening?
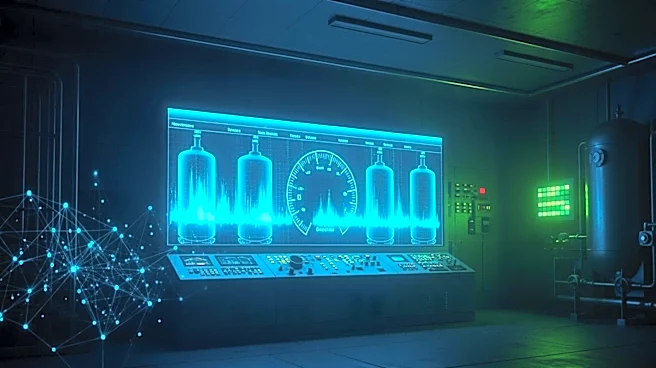
U.S. officials suspect that Iranian hackers are responsible for a series of cyber intrusions targeting systems that monitor fuel levels in storage tanks at gas stations across multiple states. These breaches exploited automatic tank gauge (ATG) systems that were
left online without password protection, allowing hackers to manipulate display readings. Although no physical damage has been reported, the potential for undetected gas leaks has raised safety concerns. The U.S. Cybersecurity and Infrastructure Security Agency has been contacted for comment, while the FBI has declined to comment. This incident is part of a broader pattern of Iranian cyber activities targeting U.S. infrastructure, including previous attacks on water utilities and attempts to influence U.S. elections.
Why It's Important?
The suspected Iranian cyber attack underscores the vulnerability of U.S. critical infrastructure to foreign cyber threats. Such breaches can have significant implications for public safety and economic stability, particularly if they lead to disruptions in fuel supply or other essential services. The incident also highlights the ongoing geopolitical tensions between the U.S. and Iran, with cyber warfare becoming a key component of modern conflicts. As the U.S. continues to enhance its domestic manufacturing and energy production capabilities, ensuring robust cybersecurity measures is crucial to protect against such threats. The attack serves as a reminder of the need for continuous vigilance and investment in cybersecurity to safeguard national infrastructure.
What's Next?
If Iran's involvement is confirmed, it could lead to increased political and economic tensions between the U.S. and Iran. The U.S. government may consider implementing stricter cybersecurity regulations and enhancing collaboration with private sector partners to prevent future attacks. Additionally, there may be calls for increased funding and resources for cybersecurity agencies to bolster defenses against foreign cyber threats. The incident could also prompt a reevaluation of current cybersecurity strategies and the development of new technologies to detect and mitigate such threats more effectively.