What's Happening?
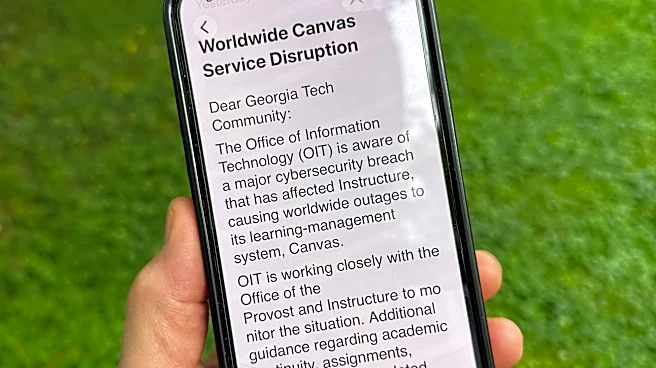
The Australian Cyber Security Centre (ACSC) has issued a warning regarding a malicious cyber campaign that utilizes the ClickFix social engineering technique to deploy the Vidar Stealer malware. This campaign is targeting infrastructure and organizations
across various sectors, including those in the United States. Vidar Stealer is an infostealer malware that primarily affects Microsoft Windows users, aiming to extract sensitive information such as usernames, passwords, credit card details, cryptocurrency wallets, browser history, and multi-factor authentication tokens. The malware has been active since 2018 and is distributed through compromised WordPress sites. These sites redirect users to malicious sites using ClickFix tactics, which involve fake CAPTCHA verification prompts to trick users into executing harmful commands. Once deployed, Vidar Stealer employs defense-evasion techniques, including self-deletion of the initial executable, allowing it to persist in memory and evade detection.
Why It's Important?
The warning from the ACSC highlights a significant cybersecurity threat that could impact U.S. infrastructure and organizations. The use of ClickFix techniques to bypass traditional cybersecurity measures poses a challenge for IT security teams. The potential theft of sensitive information can lead to financial losses, identity theft, and compromised organizational data. This situation underscores the importance of robust cybersecurity measures and awareness among users to recognize and avoid social engineering tactics. Organizations in the U.S. need to be vigilant and implement recommended security practices to mitigate the risk of such attacks.
What's Next?
Organizations are advised to follow the ACSC's guidance to counter the threat posed by Vidar Stealer and similar malware campaigns. This includes enhancing cybersecurity protocols, educating employees about social engineering tactics, and implementing advanced threat detection systems. As cyber threats continue to evolve, ongoing vigilance and adaptation of security measures will be crucial in protecting sensitive information and maintaining the integrity of organizational systems.