What's Happening?
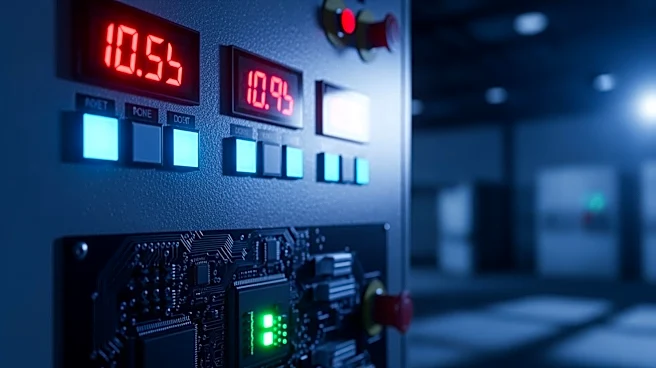
Iran-linked hackers have been identified as targeting critical infrastructure organizations in the United States, specifically focusing on industrial control systems (ICS) and operational technology (OT). According to a joint advisory from the Cybersecurity
and Infrastructure Security Agency (CISA), the FBI, and other agencies, these hackers have exploited vulnerabilities in programmable logic controllers (PLCs) from companies like Rockwell Automation and Siemens. The attacks have led to operational disruptions and financial losses by tampering with human-machine interfaces (HMIs) and supervisory control and data acquisition (SCADA) systems. The targeted sectors include government services, water, and energy. The advisory highlights the use of legitimate programming software, such as Rockwell’s Studio 5000 Logix Designer, to manipulate control systems, posing significant risks to operational safety and integrity.
Why It's Important?
The targeting of critical infrastructure by Iranian-linked hackers underscores the vulnerability of essential services in the U.S. to cyberattacks. These attacks not only threaten operational continuity but also pose significant risks to public safety and national security. The ability to manipulate control systems can lead to equipment damage and safety incidents, affecting water treatment plants and power facilities. This situation highlights the need for robust cybersecurity measures and the importance of isolating critical systems from public internet access. The advisory serves as a wake-up call for industries to strengthen their defenses and adopt zero trust architectures to protect against such sophisticated threats.
What's Next?
In response to these threats, organizations are urged to disconnect PLCs from the internet and implement strict network segmentation to protect critical infrastructure. CISA's guidance includes enabling multi-factor authentication and ensuring that remote access is secured through network proxies or gateways. However, the reliance on VPNs, which are considered insecure, remains a concern. As geopolitical tensions persist, the frequency and sophistication of such cyberattacks are expected to increase, necessitating continuous monitoring and incident response preparedness. Organizations must prioritize securing their operational technology environments to prevent further disruptions and potential safety hazards.