What's Happening?
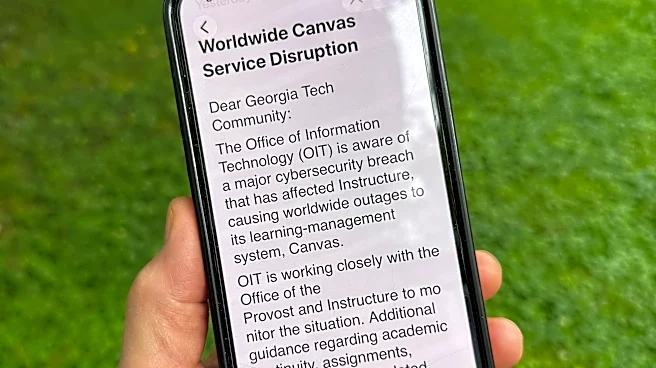
A new security vulnerability known as 'Dirty Frag' has been disclosed, affecting all major Linux distributions. This local privilege escalation bug allows users to gain root access, posing significant security risks. The vulnerability was made public
earlier than planned due to a broken embargo, leaving systems unpatched. The issue resides in the decryption fast paths of the esp4, esp6, and rxrpc kernel code. While no official patches are available yet, a workaround involves removing the affected modules. Alma Linux has released early patches for testing, but the broader Linux community remains vulnerable until official fixes are deployed.
Why It's Important?
The disclosure of the Dirty Frag vulnerability highlights critical security challenges within the Linux ecosystem. With root access potentially compromised, systems across various industries, including government, finance, and healthcare, face heightened risks of unauthorized access and data breaches. This vulnerability underscores the need for robust security protocols and timely patch management. Organizations relying on Linux must prioritize security updates and consider implementing the workaround to mitigate immediate threats. The incident also raises concerns about the effectiveness of embargoes and the coordination between security researchers and software maintainers.
What's Next?
Linux distributions are expected to release official patches to address the Dirty Frag vulnerability. Security teams will need to monitor updates closely and apply patches promptly to safeguard systems. The incident may prompt discussions on improving embargo processes and enhancing collaboration between researchers and developers. Additionally, organizations may reassess their security strategies, focusing on proactive measures to detect and respond to vulnerabilities swiftly.