What's Happening?
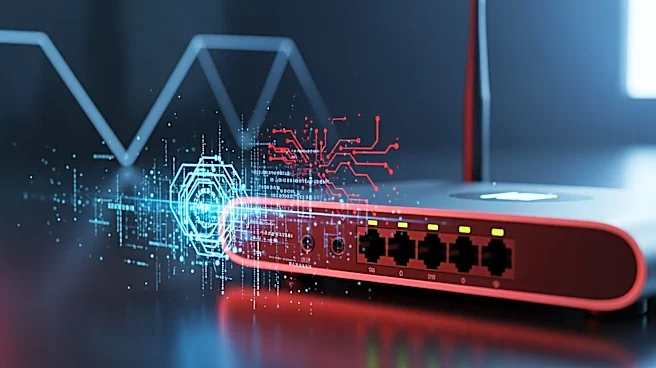
The FBI, in collaboration with the NSA and international partners, conducted Operation Masquerade to remotely patch thousands of privately-owned routers in the U.S. and other countries. This operation aimed to evict Russian military intelligence operatives,
specifically the GRU, who had been exploiting vulnerabilities in routers to redirect user traffic and harvest sensitive data. The routers, primarily from TP-Link and Mikrotik, were compromised by inserting malicious DNS resolvers. The FBI used court-authorized commands to replace these with legitimate resolvers, effectively neutralizing the threat. This operation highlights the ongoing cyber espionage activities by Russian intelligence and the proactive measures taken by U.S. law enforcement to protect national security.
Why It's Important?
The operation underscores the persistent threat posed by state-sponsored cyber espionage, particularly from Russian intelligence agencies. By targeting routers, the GRU was able to intercept sensitive data, posing a significant risk to both individual privacy and national security. The FBI's intervention demonstrates the importance of proactive cybersecurity measures and international cooperation in combating cyber threats. This operation also raises awareness about the vulnerabilities in consumer-grade routers and the need for users to maintain updated firmware and secure configurations to prevent exploitation.
What's Next?
Following the operation, users are advised to apply available firmware updates, verify DNS settings, and change default credentials to enhance security. The U.S. government may continue to monitor and address similar threats, potentially leading to further international collaborations to combat cyber espionage. Additionally, the operation may prompt discussions on the regulation and security standards for consumer-grade routers to prevent future vulnerabilities.