What's Happening?
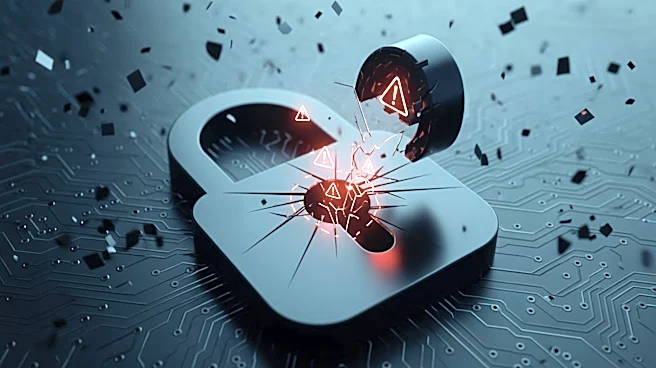
Two weeks after a significant vulnerability was discovered in Apache's ActiveMQ messaging middleware, thousands of instances remain unpatched. The vulnerability, identified as CVE-2026-34197, was revealed on April 7, and despite warnings, approximately
6,500 instances are still exposed to potential exploitation. This situation highlights a concerning trend where application developers and IT leaders are not promptly addressing security vulnerabilities. The ShadowServer Foundation's statistics underscore the urgency of the issue, as unpatched systems remain vulnerable to remote code injection attacks. IT analyst Rob Enderle emphasized the critical nature of timely patching, noting that delays in addressing such vulnerabilities can lead to severe network security risks.
Why It's Important?
The persistence of unpatched Apache ActiveMQ instances poses a significant threat to cybersecurity. In an era where cyberattacks can be rapidly weaponized, the delay in patching these vulnerabilities increases the risk of exploitation by malicious actors. This situation underscores the importance of proactive vulnerability management and the need for organizations to prioritize security updates. The potential impact on businesses and public institutions is substantial, as unpatched systems can lead to data breaches, financial losses, and reputational damage. The incident serves as a reminder of the critical role that timely security measures play in protecting digital infrastructure.
What's Next?
Organizations using Apache ActiveMQ are urged to prioritize patching the identified vulnerability to mitigate potential risks. As the cybersecurity landscape evolves, it is crucial for IT leaders to implement robust vulnerability management practices and ensure that security updates are applied promptly. The ongoing situation may prompt further scrutiny and regulatory pressure on companies to enhance their cybersecurity protocols. Additionally, the incident could lead to increased collaboration between cybersecurity firms and organizations to develop more effective strategies for addressing vulnerabilities in real-time.