What's Happening?
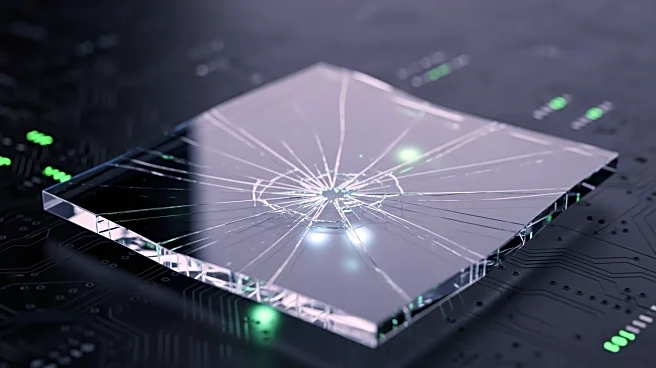
Threat actors have been exploiting extension dependency relationships within the Open VSX registry to distribute malware as part of the GlassWorm supply-chain campaign. Researchers from Socket have identified at least 72 additional malicious Open VSX extensions
linked to this campaign since January 31, 2026. These extensions masquerade as useful tools for developers, such as linters, formatters, and database utilities, but serve as conduits for a malware loader associated with the GlassWorm operation. The attackers are leveraging 'extensionPack' and 'extensionDependencies' to transform initially benign-looking extensions into vehicles for malware delivery in subsequent updates. This method allows the malware to be introduced only after trust has been established with the user.
Why It's Important?
The exploitation of Open VSX extensions by the GlassWorm campaign highlights significant vulnerabilities in software supply chains, particularly those involving developer tools. This incident underscores the risks associated with dependency management in software development, where seemingly benign components can become vectors for malicious activity. The impact is particularly concerning for developers who rely on these tools for coding and software management, as it compromises the integrity of their development environments. The broader implications for the tech industry include potential disruptions in software development processes and increased scrutiny on the security of open-source repositories. Companies and developers may need to implement more stringent security measures to protect against such supply-chain attacks.
What's Next?
In response to this threat, developers and organizations using Open VSX extensions may need to conduct thorough audits of their current tools and dependencies to identify and remove any compromised extensions. Security teams are likely to enhance monitoring and detection capabilities to identify similar threats in the future. Additionally, there may be increased collaboration between security researchers and open-source communities to develop more robust security protocols for managing dependencies. The incident could also prompt discussions on the need for improved security standards and practices in the management of open-source software repositories.