What's Happening?
Organizations across several countries, including South American nations, Bosnia, Croatia, Greece, Slovenia, and Spain, have been targeted by the Formbook information-stealing malware through sophisticated phishing campaigns. According to Infosecurity
Magazine, these attacks involve two distinct methods. The first campaign uses malicious emails with RAR attachments containing DLLs and a Windows executable file, employing DLL side-loading to execute Formbook undetected. The second campaign utilizes phishing emails with JavaScript and PDF files that conceal the malware payload. When the JavaScript is executed, it injects image files that deploy PowerShell commands, leading to the execution of a Windows executable that launches a Formbook-injecting malware loader. This loader has been previously used to deliver other malware such as AsyncRAT, Remcos, XWorm, and SmokeLoader.
Why It's Important?
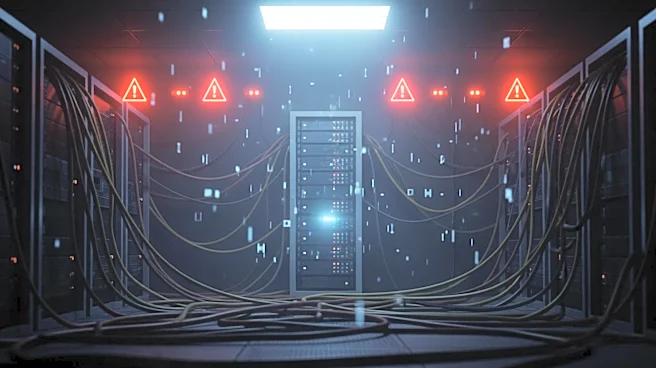
The deployment of Formbook malware in these phishing campaigns highlights the evolving threat landscape faced by organizations worldwide. The use of sophisticated techniques like DLL side-loading and PowerShell command execution underscores the need for enhanced cybersecurity measures. Organizations must be vigilant in monitoring suspicious email attachments and unusual system behaviors to prevent data breaches and information theft. The widespread nature of these attacks, affecting multiple countries and industries, indicates a significant risk to global cybersecurity. Companies that fail to address these vulnerabilities may face severe consequences, including financial losses, reputational damage, and compromised sensitive information.
What's Next?
Organizations are expected to strengthen their cybersecurity protocols in response to these threats. This includes implementing advanced monitoring systems to detect and prevent malware infiltration through email attachments and other vectors. Security teams may need to focus on identifying and mitigating manual DLL mapping symptoms and anomalous DLL loading behaviors. As the threat landscape continues to evolve, collaboration between international cybersecurity agencies and private sector companies will be crucial in developing effective countermeasures against such sophisticated attacks.