What's Happening?
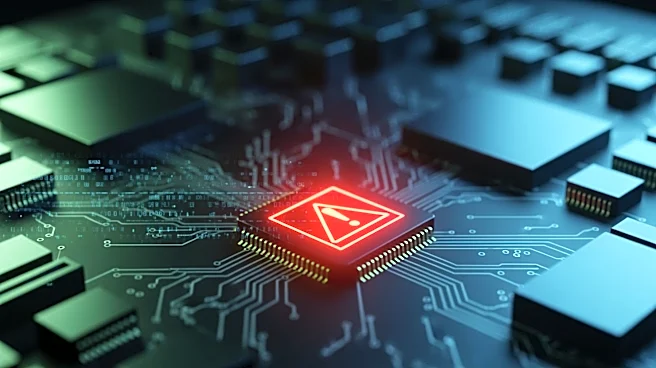
A newly identified Linux backdoor, named Quasar Linux (QLNX), is targeting software developers by stealing credentials across the software supply chain, according to Trend Micro. The RAT (Remote Access Trojan) features a modular architecture and employs
multiple persistence and detection evasion mechanisms. It is designed to steal developer credentials, keys, and tokens, potentially granting attackers access to development tools, cloud environments, and repositories. The malware targets AWS credentials, Kubernetes tokens, Docker Hub credentials, Git access tokens, NPM authentication tokens, and PyPI API keys. This could allow attackers to publish malicious packages through compromised developer accounts. The RAT operates in memory, spoofs its process name, and can delete itself to evade detection. It also performs system reconnaissance, hides specific processes, ports, and files, and clears system logs.
Why It's Important?
The emergence of QLNX poses a significant threat to the software development industry, particularly in the U.S., as it targets critical infrastructure within the software supply chain. By compromising developer credentials, attackers can potentially inject malicious code into widely used software packages, leading to widespread security breaches. This could have severe implications for businesses relying on these software tools, as it may result in unauthorized access to sensitive data and disruption of services. The ability of QLNX to persist through multiple mechanisms and evade detection makes it a formidable threat that requires immediate attention from cybersecurity professionals. Organizations must enhance their security measures to protect against such sophisticated attacks, which could have far-reaching consequences for the integrity and security of software development processes.
What's Next?
Organizations are likely to increase their focus on securing the software supply chain by implementing stricter access controls and monitoring for unusual activity. Cybersecurity firms may develop new tools and strategies to detect and mitigate threats posed by QLNX and similar malware. Additionally, there may be increased collaboration between industry stakeholders to share threat intelligence and best practices for safeguarding developer credentials. As awareness of this threat grows, software developers and companies may prioritize security training and awareness programs to prevent credential theft and ensure the integrity of their development environments.