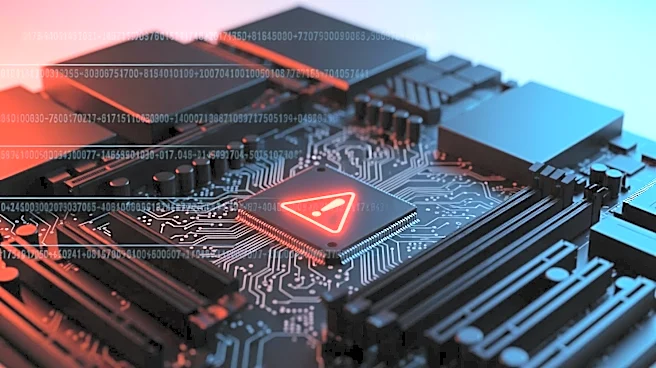
What's Happening?
A new Android banking trojan named Mirax has emerged, targeting devices across Europe. According to Infosecurity Magazine, the malware employs social engineering tactics, using illicit ads on platforms like Facebook and Instagram to redirect users to fraudulent
IPTV or streaming apps. These apps act as droppers for the Mirax malware, which is hosted on GitHub. Once installed, the malware decrypts concealed payloads and establishes WebSockets-based communication channels, allowing for remote device control and data compromise. The malware has already targeted over 200,000 accounts, primarily affecting Spanish-speaking users. The Mirax trojan is notable for its remote access and residential proxy capabilities, turning infected devices into proxy nodes for illicit traffic diversion and anonymized network attacks.
Why It's Important?
The emergence of the Mirax trojan highlights the growing sophistication and modularity of mobile security threats. By turning infected devices into residential proxy nodes, threat actors can conduct anonymized network attacks and facilitate account takeovers. This development poses significant risks to personal data security and privacy, as well as the integrity of online financial transactions. The widespread targeting of Spanish-speaking users suggests a focused attack strategy, potentially impacting a large demographic. The use of social media platforms for malware distribution underscores the need for enhanced security measures and user awareness to prevent such intrusions.