What's Happening?
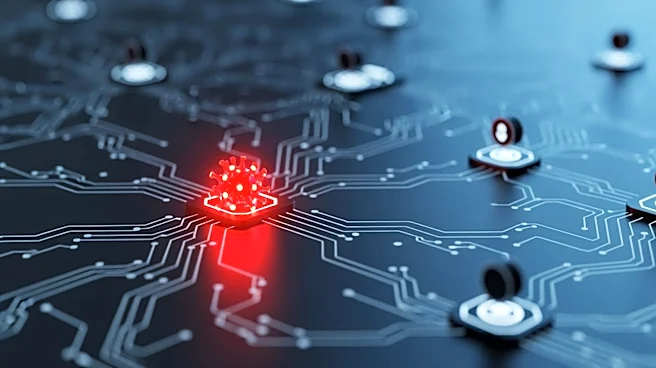
A newly identified advanced persistent threat (APT) group, dubbed GopherWhisper, has been linked to cyber attacks on government entities, utilizing legitimate services for command-and-control (C&C) communication and data exfiltration. According to ESET,
the group, operating out of China since at least November 2023, employs multiple Go-based backdoors and custom loaders. The investigation revealed that GopherWhisper targeted a Mongolian governmental organization, infecting approximately 12 systems. The group uses tools like LaxGopher, which communicates via Slack, and RatGopher, which uses Discord, to execute commands and exfiltrate data.
Why It's Important?
The activities of GopherWhisper highlight the evolving nature of cyber threats, where attackers increasingly leverage legitimate services to mask their operations and evade detection. This poses significant challenges for cybersecurity defenses, as traditional detection methods may not identify such sophisticated tactics. The targeting of government entities underscores the potential risks to national security and the need for enhanced cybersecurity measures. The incident also raises concerns about the broader implications of state-sponsored cyber activities and the necessity for international cooperation in addressing these threats.